The Cost of Undiscovered Breaches
4,388
$10.22M
+23%
$4.02M
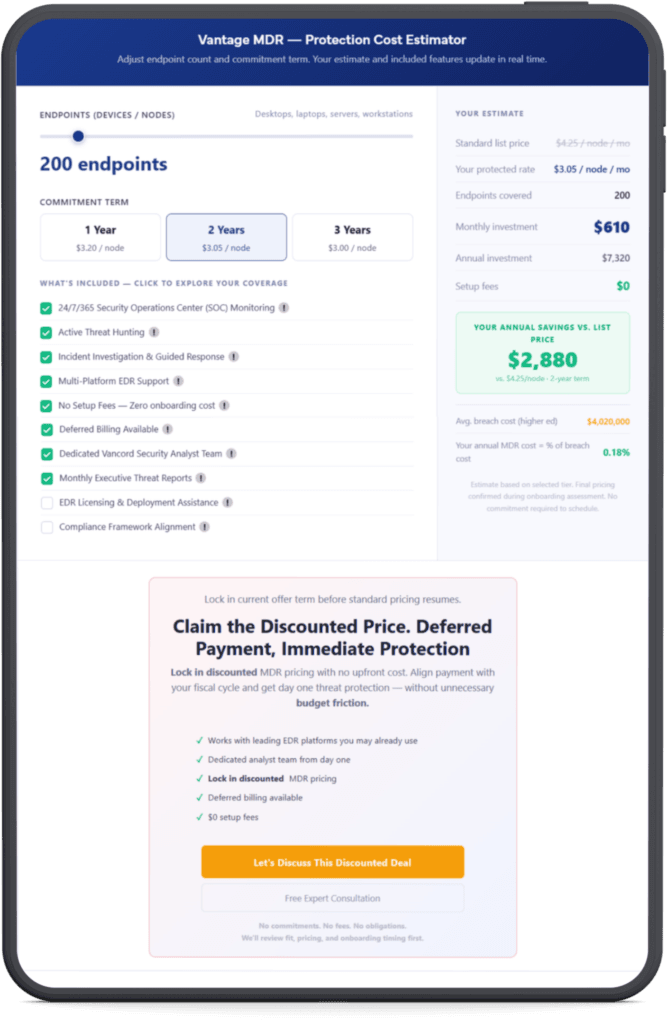
Vantage MDR — Protection Cost Estimator
Adjust endpoint count and commitment term. Your estimate and included features update in real time.
- 24/7/365 Security Operations Center (SOC) Monitoring!
- Active Threat Hunting!
- Incident Investigation & Guided Response!
- Multi-Platform EDR Support!
- No Setup Fees — Zero onboarding cost!
- Dedicated Vancord Security Analyst Team!
- Monthly Executive Threat Reports!
- Deferred Billing Available!
- EDR Licensing & Deployment Assistance!
- Compliance Framework Alignment!
Estimate based on selected tier. Final pricing confirmed during onboarding assessment. No commitment required to schedule.
Why Breaches Show Up in the Fall
This is not a seasonal attack pattern. It is a detection lag pattern. Attackers enter during your minimum-staffed period. By the time your full team is back and looking closely, the attacker has been inside for months. The discovery happens in the fall. The breach happened in the summer. The two events feel connected. They are not.
| MAY – JUN | Attacker gains access. Staff coverage drops 30 to 40 percent. Alert queues go unreviewed. |
| JUL – AUG | Lateral movement. Credential harvesting. Data exfiltration begins. Team is at minimum capacity. |
| SEP | Staff return. The breach is still active. Damage accumulates in the background. |
| OCT – NOV | Anomalies get flagged. Investigation starts. Average time since initial access: 181 days. |
| DEC–APR | Breach disclosed. Remediation begins. Average cost: $4 to $10 million. Recovery takes 100 or more days. |
The Risk Is Not the Same in Every Sector
Select your sector to see the specific threats, compliance obligations, and attack patterns relevant to your environment.
-
 Higher Education
Higher Education -
 K-12 Education
K-12 Education -
 State & Local Gov
State & Local Gov -
 Manufacturing
Manufacturing -
 Healthcare
Healthcare -
 Logistics
Logistics -
 Finance
Finance
Higher Education
Universities hold more personal data than most organizations their size, operate largely open networks, and typically run with limited dedicated security staff. In 2025, US higher education institutions had 3.7 million records breached. The combination of open access, minimal monitoring, and a compressed summer window makes this sector one of the most targeted in the country.
Compliance obligations:
FERPA (student records) HIPAA (campus health) GLBA (financial aid) State breach notification laws
Primary attack vectors
- AI-written phishing targeting faculty, HR, and financial aid staff. Education phishing rose 224 percent in 2024.
- Ransomware against learning management systems and research databases
- Third-party vendor breaches cascading through shared platforms such as PowerSchool, Oracle, and MOVEit
- Credential theft targeting student, alumni, and staff accounts
- Research IP theft by criminal groups and state-sponsored actors
K-12 Education
82 percent of US school districts experienced a cyber incident between July 2023 and December 2024. Ransomware groups have lowered their demands in the education sector specifically because smaller amounts are more likely to get paid from constrained budgets. The attack volume stayed flat. The targeting became more precise.
Compliance obligations:
FFERPA COPPA (students under 13) State student privacy laws E-Rate cybersecurity requirements
Primary attack vectors
- Ransomware taking district operations offline for days or weeks at a time
- Supply chain attacks through shared student information systems and EdTech platforms
- Phishing targeting administrative staff and HR payroll access
- Student PII exposure triggering regulatory investigations and legal action
- Summer window attacks when districts operate with skeleton IT coverage
State and Local Government
Most municipal governments and state agencies have fewer than five dedicated cybersecurity staff. The data they hold is sensitive, the systems are often old, and a successful attack does not just create a data problem. It disrupts public services. 911 dispatch, permitting systems, utility billing, emergency management. The stakes are not abstract.
Compliance obligations:
CJIS (law enforcement data) State cybersecurity frameworks HIPAA (public health services) Federal grant compliance
Primary attack vectors
- Ransomware against aging infrastructure and unpatched systems
- Spear-phishing targeting finance officers, administrators, and elected officials
- Disruption of emergency services including 911, fire dispatch, and EMS
- Citizen data theft from tax systems, permit databases, and utility billing
- Credential compromise through public-sector procurement portals
Manufacturing and Defense Supply Chain
Defense contractors face two distinct threat categories. Criminal groups looking to encrypt production systems for ransom. State-sponsored actors looking for design files, contract data, and proprietary processes. CMMC 2.0 compliance is now a prerequisite for DoD contract participation. A single undetected breach can cost a manufacturer both their data and their eligibility to bid.
Compliance obligations:
CMMC 2.0 and NIST 800-171 ITAR DoD contract security requirements State cybersecurity directives
Primary attack vectors
- OT and ICS attacks targeting production lines and SCADA environments
- State-sponsored intellectual property theft targeting design files and formulas
- Supply chain compromise through subcontractor credentials
- Ransomware shutting down assembly operations. Average cost per incident: $2.8 million.
- CMMC audit failure resulting in contract disqualification
Healthcare and Life Sciences
Healthcare breaches cost an average of $7.42 million per incident in 2025, the highest of any sector. When clinical systems go offline, patient care is directly affected. Smaller practices and regional hospitals face the same threat actors as large health systems but with a fraction of the security resources.
Compliance obligations:
HIPAA and HITECH State patient data laws FDA cybersecurity guidance for medical devices 21 CFR Part 11
Primary attack vectors
- Ransomware disabling electronic health record systems with direct patient safety consequences
- Pharmaceutical and clinical research IP theft
- Credential phishing targeting clinical staff and billing departments
- Medical device network compromise
- HIPAA violation penalties up to $1.9 million per violation category
Logistics and Transportation
Logistics companies run on tight margins. A 48-hour outage in warehouse management or fleet routing does not stay contained. It cascades through delivery commitments, customer contracts, and partner relationships. These companies are deeply technology-dependent but rarely have dedicated security staff.
Compliance obligations:
TSA cybersecurity directives CTPAT (customs-trade partnership) DoT data requirements State breach notification
Primary attack vectors
- Ransomware targeting warehouse management, transportation management, and ERP systems
- Fleet routing and telematics system compromise
- Vendor credential theft enabling supply chain infiltration
- Financial fraud through compromised billing and procurement portals
- IoT device compromise in warehouse and distribution environments
Finance and Insurance
Financial firms are targeted because the path from breach to cash is short. Regional firms and insurance agencies carry the same data richness as large banks but operate with far less security infrastructure. A credential breach at a small advisory firm can expose client portfolios, wire transfer access, and years of transaction history in a single event.
Compliance obligations:
TSA cybersecurity directives CTPAT (customs-trade partnership) DoT data requirements State breach notification
Primary attack vectors
- Business email compromise targeting wire transfer authorization
- Spear-phishing against advisors with access to client accounts
- Client portfolio and PII exfiltration
- Third-party custodian and SaaS platform compromise
- SEC mandatory disclosure failures triggering regulatory action
What Happens When You Activate Vantage MDR
No new hardware. No platform replacement. Works with SentinelOne, CrowdStrike, Microsoft Defender, and other endpoint detection tools you may already run. If you do not have an EDR solution in place, we can help with licensing and deployment before onboarding.
- Works with leading EDR platforms you may already use
- Dedicated analyst team from day one
- Lock in discounted MDR pricing
- Deferred billing available
- $0 setup fees
No commitments. No fees. No obligations.
We'll review fit, pricing, and onboarding timing first.
Frequently Asked Questions
- Antivirus blocks known threats based on signatures. Endpoint detection tools flag suspicious behavior and generate alerts. MDR adds the human layer: trained analysts who investigate those alerts around the clock, determine whether a threat is real, and respond when it is. Most breaches that go undetected for months do so because the alerts existed but no one investigated them. MDR closes that gap.
- No. Vantage MDR works with SentinelOne, CrowdStrike, Microsoft Defender, and other leading endpoint tools. We connect to your existing platform and layer analyst coverage on top of it. You keep what you have. You add the 24-hour human monitoring that makes it effective.
- The IBM 2025 Cost of a Data Breach Report puts the average at 181 days. That is six months of an attacker inside your network before anyone knows. In the education sector, these breaches typically begin during summer when staff coverage is lowest and are discovered in the fall when full teams return and look more carefully. MDR does not wait for someone to notice. It monitors continuously.
- Three reasons. First, they hold large amounts of personal data: student records, research, financial aid, citizen information. Second, they run open or semi-open networks with many users and limited access control. Third, most operate with small IT teams and no dedicated security staff. Attackers choose targets where the effort-to-reward ratio is favorable. Understaffed institutions with valuable data are at the top of that list.
- We investigate first. When an alert triggers, an analyst reviews it and determines whether it is a real threat or a false positive. If it is real, we work through containment with your team: isolating affected systems, identifying the scope of access, and documenting the incident. You receive a full incident report. We do not send alerts and wait for you to figure out what to do next.
- Onboarding typically takes a few days. We connect to your existing EDR platform, configure alert routing, and run an initial baseline review of your environment. No hardware is shipped. No major changes to your infrastructure. Monitoring begins after onboarding is complete. If you do not have an EDR in place, we can assist with selection, licensing, and deployment before onboarding starts.
- The per-node model scales down as well as up. A 100-endpoint organization at the 1-year rate pays $320 per month. A 500-endpoint organization pays $1,600 per month. Deferred billing is available to align payments with your fiscal year. Many smaller institutions use the calendar window before fiscal year-end to get a contract in place so coverage is active from the start of the next cycle.
- Attackers who have successfully breached an organization once often return. Beyond that, the techniques in use today are more automated and AI-assisted than even two years ago. A prior breach does not reduce your attack surface. It may increase it if credential data was exposed and has been circulating since. Ongoing monitoring catches re-entry attempts and new attack vectors that your existing tools may not flag without human review.
- We work with organizations operating under FERPA, HIPAA, CMMC 2.0, NIST 800-171, CJIS, GLBA, and state-level frameworks. MDR coverage supports your compliance posture by providing continuous monitoring logs, incident documentation, and the audit trail that assessors look for. We do not provide compliance certification, but we provide the operational controls that support it.
- A senior security analyst costs $90,000 to $130,000 per year in salary alone, works business hours, takes time off, and covers one environment. Vantage MDR provides a full analyst team watching your environment 24 hours a day, seven days a week, including nights, weekends, and your entire summer staffing gap. For most organizations in this size range, a full in-house security operations capability is not practical. MDR is what fills that gap.
- Commitment terms lock in the discounted pricing. The 3-year rate of $3.00 per node is available because of the certainty that term provides. If your situation changes, contact your Vancord representative. The specifics of any mid-term change are handled in the service agreement.
- After July 31, standard contract rates remain available to eligible organizations, but the additional term-based discounts are specific to this window. If you are in a budget process or need more time, reach out before the deadline. We can often work with fiscal year constraints, particularly when deferred billing is part of the arrangement.