Overview
Ball Chain is a well-known U.S. manufacturer with multiple divisions, hundreds of employees, and a unique product line used around the world. From military dog tags to the chains attached to bank pens, their products are everywhere, and their operations rely on uninterrupted access to digital tools, secure communication, and safe remote connectivity.
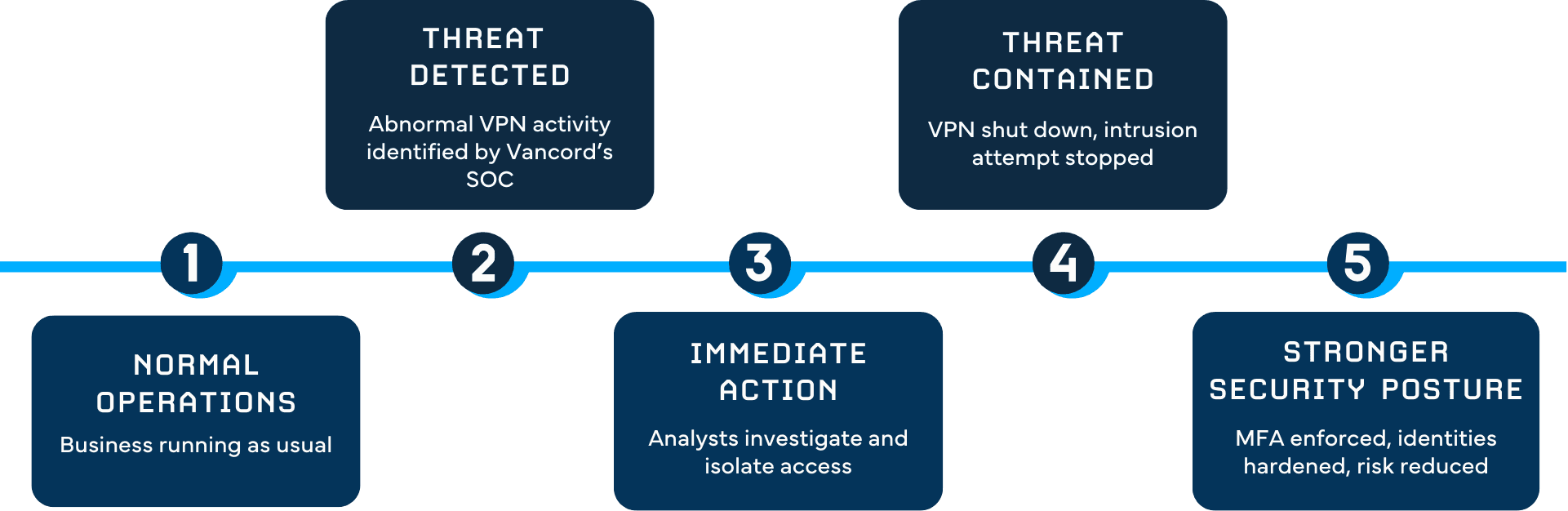
But like many manufacturers with fast-moving operations, Ball Chain faced growing cybersecurity risks. Legacy VPN access, weak passwords, and outdated authentication practices left the door open for attackers. And one quiet weekend, that door almost opened.
Thanks to Vancord’s Security Operations Center (SOC), an active intrusion attempt was detected, investigated, and contained before any damage occurred. A serious threat was blocked before it caused any damage, keeping the company’s operations running smoothly.
The Challenge
Before this event, Ball Chain’s environment had a mix of old and new systems. Some users had accounts in multiple divisions. Several passwords never expired. VPN access lacked multi-factor authentication (MFA). And like many manufacturing companies, most critical systems were used heavily but updated slowly.
The company understood these risks, but implementing changes across several divisions required time and coordination.
Then, one weekend, everything changed.
Vancord’s SOC received unusual login alerts from Ball Chain’s VPN, repeated authentication attempts, access failures, and activity across both servers and workstations. Automated protections began isolating user accounts, signaling that something serious was happening.
If attackers gained access to one account, they could attempt to move deeper into the network, reach internal systems, or compromise sensitive files. Remote access was the primary risk point, and the pressure was high. It was a real-time situation that required immediate action, no matter the day or hour.
Ball Chain was not aware anything was wrong yet. Their systems appeared normal from the outside.
Inside the network, however, something was brewing.
Solutions
Vancord’s SOC moved quickly, combining real-time monitoring with hands-on investigation. Three major areas of action helped protect Ball Chain before the situation escalated.
1. Rapid Detection and Immediate Containment
Vancord’s SOC tools picked up the threat long before the client noticed anything. Automated alerts flagged suspicious activity coming from the company’s VPN range, attempts to authenticate, patterns that looked abnormal, and behavior Defender categorized as potentially malicious.
Within minutes:
- The SOC reviewed activity logs
- Pulled in additional analysts for support
- Confirmed that multiple user accounts were being targeted
- Noticed attempted access to internal systems
The team made a fast decision: shut down the VPN completely.
This move stopped the attacker instantly. With the VPN offline, the path into the network was closed, and the threat was contained.
The SOC then called Ball Chain to inform them of the situation and explain next steps. Even though it was a weekend, communication was clear, fast, and direct.
2. Security Hardening and Password Reset
Once the environment was contained, the next step was strengthening identity security, the core target of the attack.
Vancord worked with Ball Chain to:
- Remove all “password never expires” settings
- Increase password complexity to 12 characters
- Reset all user passwords across the entire organization
- Validate all active accounts and remove unused ones
These changes eliminated long-standing vulnerabilities that attackers often exploit.
With stronger identity controls and fresh password policies, Ball Chain’s user accounts became significantly harder to compromise.
3. VPN Reinforcement and Mandatory MFA
The SOC rebuilt VPN access from the ground up to ensure the attacker could not re-enter.
Key updates included:
- Creating completely new VPN accounts
- Using secure local accounts instead of older configurations
- Adding one-time password (OTP) MFA for every VPN login
- Ensuring only essential staff had access during investigation
- Coordinating with infrastructure to deploy MFA across the organization
Whether using Duo or Microsoft Authenticator, every user now needed MFA to log in. This change alone dramatically reduced the chance of any future breach.
Results
Within days, Ball Chain’s VPN was back online, stronger, more secure, and fully protected by MFA.
Most importantly:
- No systems were compromised
- No data was accessed
- No downtime impacted production
- The attempted intrusion was fully contained
- Ball Chain gained confidence in Vancord’s monitoring and response
What could have become a costly breach turned into a moment of reassurance: the right technology and the right team were watching.
Conclusion
The Ball Chain cyber incident is a powerful reminder that real threats don’t wait for business hours, and that manufacturing companies are increasingly targeted by attackers looking for easy entry points.
What made the difference was Vancord’s combination of:
- 24/7 real-time SOC monitoring
- Fast incident response
- Clear communication
- Strong identity and access controls
- A team that cares enough to act immediately
Vancord didn’t just stop a threat. We helped Ball Chain strengthen their entire security foundation, reduce future risk, and gain confidence that someone is always watching their environment.
For manufacturers seeking reliable protection, responsive support, and a partner who acts before damage occurs, Vancord delivers exactly what modern businesses need: proactive security, real partnership, and peace of mind.