
When a cyber attack hits, every minute matters. The longer a threat stays in your systems, the more damage it can cause. Files can be locked. Data can be stolen. Operations can stop. Fast incident response is not just a technical goal. It protects your business, your clients, and your reputation. So how fast should incident response really be during a cyber attack?
Why Speed Matters in Incident Response
Most cyber attacks do not look dramatic at first. There is no loud warning. No flashing screen. It often starts with something small. A stolen password. A fake email that tricks someone. A hidden program running quietly.
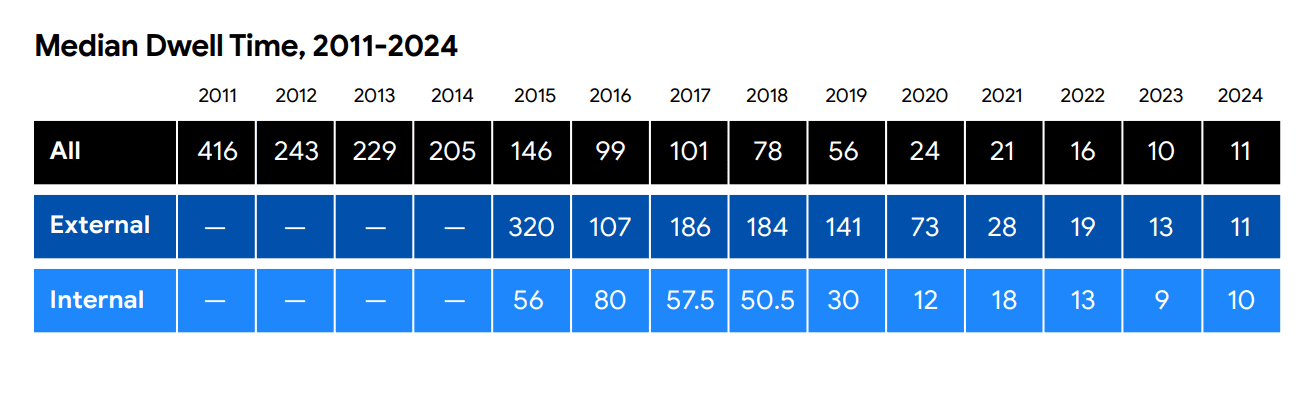
According to the 2025 Mandiant M-Trends Report, the global median dwell time for attackers was 11 days. That means many organizations did not realize someone was inside their systems for over two weeks.
Source: Mandiant M-Trends 2025 Report
Eleven days is a long time for an attacker to explore your network.
The longer attackers stay inside, the more likely they are to move across systems, escalate privileges, and steal sensitive data. Fast detection reduces that window.
At Vancord, this is why our Incident Response Services focus on early detection and rapid containment. Waiting is expensive. Acting fast is protective.
global median dwell time: middle value of time (measured in days) that cyber attackers remain undetected within a compromised network.
What Is a Cyber Security Incident Responder?
Many people search this question because they want to understand who handles cyber attacks in real life.
A cyber security incident responder is a trained professional who investigates security alerts, confirms threats, and stops attacks before they spread. They review logs, isolate devices, block malicious traffic, and guide recovery.
Inside a Security Operations Center, incident responders work around the clock. Through Vancord’s SOC services, analysts monitor systems in real time and respond when suspicious behavior appears.
Without trained responders, companies often rely on internal IT staff who may already be busy managing daily operations. That delay increases risk.
Shorter dwell time = less damage.
How Fast Should Incident Response Be?
There are three timeframes that matter during a cyber attack.
First is detection time. Ideally, suspicious activity should be identified within minutes or hours, not days.
Second is response time. Once a threat is confirmed, containment should begin immediately. That may mean isolating a device, disabling a user account, or blocking network access.
Third is recovery time. Systems should be restored safely and securely with verified clean backups.
The U.S. Cybersecurity and Infrastructure Security Agency recommends that organizations develop and regularly test an incident response plan for cyber attacks to improve reaction speed.
Source: CISA Incident Response Plan (IRP) Basics
In real terms, strong organizations aim to detect suspicious activity within the same business day and contain confirmed threats within hours.
The Cost of Waiting
Delays are expensive.
According to the IBM Cost of a Data Breach Report 2025, organizations that fully deployed security AI and automation reduced breach costs by an average of 1.9 million dollars compared to those without it.
Source: IBM Cost of a Data Breach Report 2025
Why? Because automation speeds up investigation and response.
Fast action limits:
- Data loss
- Legal exposure
- Operational downtime
- Reputation damage
For industries like healthcare, public sector, and manufacturing, even a few hours of downtime can disrupt critical services. That is why many organizations in these sectors invest in Managed Security Services and continuous monitoring.
Speed protects business continuity.
Why an Incident Response Plan for Cyber Attacks Is Critical
You cannot respond quickly if you are deciding what to do in the middle of the crisis.
An incident response plan for cyber attacks clearly defines:
Who investigates alerts
Who approves system shutdown
Who communicates with customers
Who contacts legal or compliance teams
Without a plan, people hesitate. That hesitation costs time.
Through Vancord’s Incident Ready Program, organizations build and test a documented cyber attack incident response guide before something happens. We have seen through our case studies that clients with structured response workflows recover faster and communicate more clearly during incidents.
Preparation builds confidence. Confidence improves speed.
Why 24/7 Monitoring Makes a Real Difference
Cyber attacks do not wait for business hours.
If an attacker gains access at 2 a.m., waiting until 9 a.m. can mean seven hours of unchecked damage. That is why 24/7 monitoring through a Managed Security Services program matters.
Verizon’s 2025 Data Breach Investigations Report found that stolen credentials and phishing remain among the most common initial attack methods.
These types of attacks often trigger subtle warning signs, such as unusual login activity or strange data transfers. A monitored environment catches these signals faster.
That is why 24/7 monitoring through Security Event Monitoring and a Security Operations Center is so important. Alerts are reviewed immediately. Suspicious behavior is investigated in real time.
The goal is simple. Shrink the gap between detection and response.
That gap is where financial losses grow.
Real-World Example: Ransomware Spread
Picture this.
An employee clicks a phishing link. Malware begins encrypting shared drives. If the attack is detected early, encryption can be stopped before backups are affected. If detection is delayed, full system restoration may be required.
The Cybersecurity and Infrastructure Security Agency reports that ransomware attacks continue to target organizations of all sizes, often causing operational shutdowns.
This is not only an IT issue. It is a leadership issue.
Fast response protects payroll systems, customer records, and production lines.
What Good Incident Response Looks Like
Strong incident response feels organized, not chaotic.
There is a clear escalation path. Leadership is informed quickly. Evidence is collected properly. Systems are isolated without causing unnecessary disruption.
After the threat is removed, teams review what happened. Controls are improved. Employees may receive updated security awareness training. Lessons are documented.
This continuous improvement mindset is built into how Vancord approaches cybersecurity. Incident response is not a one-time service. It connects with vulnerability management, compliance alignment, and long-term risk reduction.
FAQ: Cyber Attack Incident Response
What is a cyber attack incident response guide?
It is a documented process that explains how your organization detects, responds to, and recovers from cyber threats. It ensures everyone knows their role during a crisis.
How fast should a company respond to a cyber attack?
Detection should happen within hours when possible. Containment should begin immediately after confirmation. The faster you isolate the threat, the lower the impact.
Do small and mid-sized businesses need this?
Yes. Small and mid-sized businesses are often targeted because attackers believe defenses are weaker. Having a tested incident response plan levels the playing field.
Final Thoughts: Speed Is Protection
Cyber attacks are not rare events anymore. They are regular business risks.
The difference between a minor incident and a major breach often comes down to one factor: speed.
If you are unsure how quickly your organization would identify a threat, or if you do not have a tested incident response plan for cyber attacks, now is the time to evaluate your readiness.
You can explore Vancord’s Incident Response Services, learn more about our Security Operations Center, or connect directly through the Contact page to start the conversation.
The faster you can detect and respond, the safer your business will be.