
Manufacturing companies keep the world and U.S. Military running. They build the products we use every day. But right now, they are also one of the biggest targets for ransomware attacks. When production stops, revenue stops. Cyber criminals understand this pressure. That is why manufacturers are being hit harder than many other industries. Knowing why this is happening and how to respond can protect your operations before downtime turns into disaster.
Manufacturing Is Now a Top Ransomware Target
Ransomware attackers focus on industries where downtime is expensive. Manufacturing sits at the top of that list.
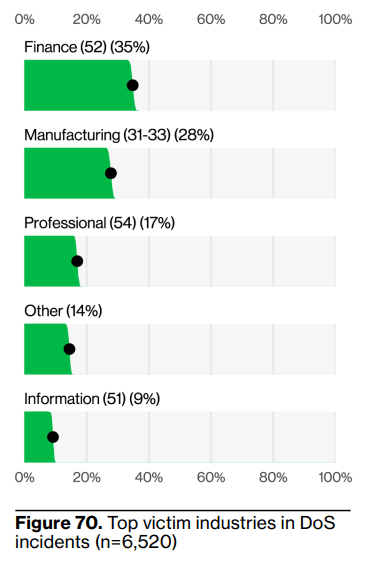
According to the 2025 Verizon Data Breach Investigations Report, manufacturing continues to be one of the most targeted industries for ransomware and extortion attacks. Ransomware represents a significant share of confirmed breaches in industrial sectors.
Source: 2025 Verizon Data Breach Investigations Report
The reason is simple. When a production line stops, every minute costs money.
The Cybersecurity and Infrastructure Security Agency has also warned that ransomware groups increasingly target critical manufacturing infrastructure because of its impact on supply chains and economic stability.
For attackers, manufacturing is not random. It is strategic.
The Real Cost of Ransomware in Manufacturing
The cost of ransomware goes far beyond the ransom demand.
Production stops. Machines cannot access control systems. Inventory data may be locked. Shipping schedules fall behind. Vendors cannot connect.
IBM’s Cost of a Data Breach Report shows that ransomware remains one of the most financially damaging types of cyber incidents due to business disruption and recovery costs.
For manufacturers, that disruption multiplies quickly. A single day of downtime can mean missed contracts, lost revenue, and long-term customer trust issues.
This is why many manufacturers are now investing in stronger Managed Security Services and proactive monitoring instead of waiting for an incident to happen.
Why Manufacturing Environments Are More Vulnerable
Manufacturing companies operate in a unique technology environment.
Most facilities run a mix of IT systems and operational technology. Office networks connect with industrial control systems. Email systems connect with production scheduling tools.
This creates complexity.
Many operational systems were built for reliability, not cybersecurity. Some machines cannot easily be patched. Others rely on legacy protocols.
Add third-party vendors, remote maintenance providers, and supply chain integrations, and the attack surface grows quickly.
At Vancord, through our Manufacturing cybersecurity services, we often see limited visibility between business networks and production systems. Without centralized Security Event Monitoring driven by a complete Cyber-Security program, unusual activity inside those environments can go unnoticed.
How Ransomware Attacks Usually Start
Most ransomware incidents start with small entry points.
The Verizon DBIR report continues to show that stolen credentials and phishing emails are among the most common initial access methods.
An attacker may gain access through:
- Compromised login credentials
- Exposed remote access systems
- Unpatched vulnerabilities
Once inside, they do not launch ransomware immediately. They explore. They map systems. They escalate privileges.
This period is known as dwell time.
According to the 2025 Mandiant M-Trends Report, the global median dwell time was 11 days. That means attackers often sit inside networks for more than two weeks before being detected.

Source: 2025 Mandiant M-Trends Report
For manufacturers, 11 days of undetected access is extremely dangerous.
What Ransomware Looks Like on a Factory Floor
When ransomware spreads inside a manufacturing company, it affects more than computers.
Here is what can happen:
| Impact Area | What Happens |
|---|---|
| Production Systems | Machines lose access to scheduling data |
| Supply Chain | Vendor integrations stop working |
| Inventory Systems | Tracking becomes unavailable |
| Shipping | Orders cannot be processed |
| Financial Operations | Billing and payroll may be delayed |
The real cost is operational paralysis.
This is why ransomware in manufacturing is both a cybersecurity issue and a business continuity issue.
How Manufacturing Companies Can Reduce Ransomware Risk
Protection starts with visibility and response speed.
Manufacturers should focus on:
- 24/7 monitoring through a Security Operations Center
- Continuous vulnerability management
- Network segmentation between IT and OT systems
- Multi-factor authentication for remote access
- A tested incident response plan
Through Vancord’s Managed Security Services and SOC solutions, manufacturing clients gain real-time monitoring instead of relying only on traditional firewalls.
Incident Response Services are equally critical. If ransomware is detected, isolation must happen quickly to prevent spread to production systems.
Our Incident Ready approach helps manufacturers test scenarios before an actual attack occurs.
Preparation reduces downtime.
Why Business Continuity Planning Is Essential
Manufacturers depend on uptime. Even a few hours of disruption can cause missed deadlines and contract penalties.
IBM’s research highlights that organizations with faster containment times experience lower overall financial impact.
Speed depends on preparation.
This connects cybersecurity directly to business resilience.
For manufacturers working with defense supply chains or public sector contracts, compliance requirements add another layer of responsibility. Aligning cybersecurity controls with industry regulations protects both operations and reputation.
The Strategic Shift: From Reactive to Proactive
In the past, many manufacturers relied on internal IT teams and basic security tools.
Today, ransomware groups operate like organized businesses. They use automation, double extortion tactics, and supply chain targeting.
That is why cybersecurity must be strategic.
Manufacturers that invest in:
- Security Operations Center monitoring
- Threat detection and response
- Regular security assessments
- Clear escalation procedures
recover faster and experience less disruption.
Through Vancord’s case studies in regulated industries, we consistently see that structured security programs shorten recovery time and reduce operational chaos during incidents.
FAQ: Manufacturing and Ransomware
Why are manufacturing companies prime ransomware targets?
Because downtime costs them money quickly. Attackers know production delays increase pressure to pay.
How can manufacturers lower ransomware risk?
By implementing 24/7 monitoring, network segmentation, vulnerability management, and a tested incident response plan.
Does ransomware only affect large factories?
No. Small and mid-sized manufacturers are frequently targeted because attackers assume defenses are weaker.
Building a Stronger Security Foundation
Manufacturing companies power the global economy. Protecting them requires more than antivirus software.
It requires structured cybersecurity designed around visibility, detection, and rapid containment.
If your organization operates in the manufacturing sector, exploring Vancord’s Manufacturing cybersecurity services is a smart next step.
You can also connect directly through the Contact page to discuss a ransomware readiness assessment.
Ransomware attackers move quickly. The right security strategy moves faster.