
Security systems create thousands of logs every day. Login attempts, firewall alerts, system updates, and application activity all generate records. The challenge is not collecting data. The real challenge is knowing which logs actually help detect cyber threats and which ones simply create noise. Many security teams spend hours reviewing alerts that never become real incidents. When organizations focus on the right security logs, they can detect attacks earlier, investigate threats faster, and reduce wasted effort.
Why Security Logs Are Important for Cybersecurity Monitoring
Security logs act like a digital record of everything happening inside a network. Every login, file access, configuration change, or network connection leaves a trace behind.
These records help a cybersecurity analyst understand how systems behave during normal operations and what changes when suspicious activity occurs.
When attackers attempt to break into a network, their actions almost always appear in logs. A sudden login from another country, a new administrator account, or a strange connection to an external server may all signal early stages of an attack.
Many organizations collect and analyze logs using a Security Information and Event Management platform, often called a SIEM. These platforms gather logs from servers, endpoints, firewalls, and cloud environments so security teams can monitor activity in one place.
The importance of monitoring logs is clear when looking at global cyber incident data. The 2025 Verizon Data Breach Investigations Report found that stolen credentials remain one of the most common ways attackers gain access to systems. Many of these incidents begin with login activity that could be identified through authentication logs.
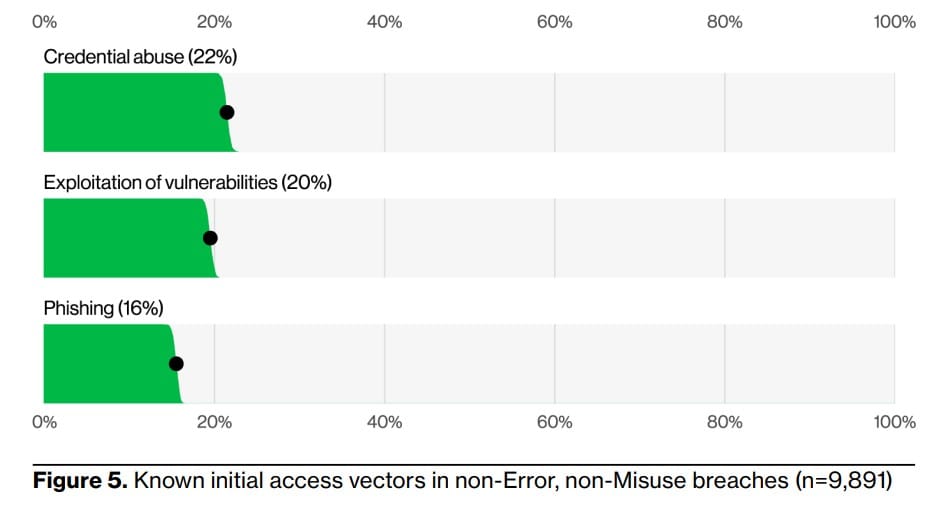
Source: 2025 Verizon Data Breach Investigations Report
Security Logs That Help Detect Real Threats
Not every log has the same value when it comes to detecting cyber attacks. Some types of logs consistently help information security analysts identify suspicious behavior early.
One of the most valuable sources is authentication logs. These records show when users log in, from which location, and from which device. Unusual login patterns often reveal credential theft or account compromise.
Network activity logs are also critical. Firewalls and network monitoring tools record connections between systems. When a device suddenly communicates with unknown servers or sends large amounts of data outside the network, analysts may investigate possible malware or data exfiltration.
Another key source is endpoint logs. These logs record activity on computers and servers, such as software installations, file access, and system processes. Endpoint logs help analysts detect malware infections, unauthorized programs, and suspicious system changes.
Cloud activity logs have become just as important. As organizations move applications to cloud platforms, logs from cloud services show user activity, configuration changes, and access to sensitive data.
When analysts combine authentication logs, network logs, endpoint logs, and cloud activity logs, they gain a clear picture of what is happening across the environment.
Many organizations rely on Managed Detection and Response services to continuously analyze these logs and identify threats before they cause damage. These services combine monitoring technology with experienced analysts who investigate suspicious behavior around the clock.
The Logs That Often Create Noise
While some logs help detect attacks, others generate large amounts of data with little security value.
For example, debug logs are designed for developers who troubleshoot software problems. These logs contain detailed technical information, but they rarely provide signals that help identify cyber threats.
Routine system health logs can also create unnecessary noise. These logs often record normal operations such as scheduled updates, background processes, or automated system checks.
Another common challenge is duplicate logging. In complex IT environments, the same event may be recorded by several tools at once. A single login attempt could appear in an endpoint log, a domain controller log, and a cloud access log. Without proper filtering, security teams may investigate the same event multiple times.
The goal is not to remove logs entirely. The goal is to prioritize the logs that reveal suspicious behavior while filtering events that do not provide meaningful security insights.
Organizations often refine this process through security event monitoring strategies, where logs are collected, correlated, and analyzed to detect threats more efficiently.
How Security Analysts Turn Logs into Threat Detection
Logs become powerful only when analysts know how to interpret them.
Inside a security operations center, a security analyst reviews alerts generated by monitoring systems. When a suspicious event appears, the analyst begins investigating the logs connected to that alert.
First, analysts determine whether the activity is normal. If a login occurs from a known employee device during regular work hours, it may be harmless. But if that same account logs in from another country in the middle of the night, it deserves investigation.
Next, analysts review related logs to see if the activity spread to other systems. Attackers often move through a network after gaining initial access. Logs may show attempts to access other servers, create new accounts, or transfer sensitive data.
Finally, analysts determine whether the activity caused real damage. If logs show that files were accessed, permissions changed, or malware installed, the event may become a full security incident.
Guidance from the National Institute of Standards and Technology Log Management Guide emphasizes that organizations must regularly review and correlate logs across systems to detect threats effectively.
Building a Smarter Log Monitoring Strategy
Many organizations collect far more logs than they can realistically analyze. This often leads to alert fatigue, where security teams become overwhelmed by constant notifications.
A stronger strategy focuses on visibility and prioritization.
Security teams should prioritize logs that show:
- user authentication activity
- network connections between systems
- endpoint behavior and system changes
- access to sensitive data
These events provide the clearest signals of attacker behavior.
Automation also plays an important role. Modern security platforms use behavioral analytics and threat intelligence to filter routine activity while highlighting events that may indicate an attack.
This is why many companies combine log monitoring with continuous threat detection through managed security services. By combining technology with experienced analysts, organizations gain faster insight into potential attacks.
According to IBM Cost of a Data Breach Report, organizations that detect and contain breaches faster significantly reduce the overall financial impact of an incident.
Vancord has worked with organizations across healthcare, manufacturing, and public sector environments to strengthen their monitoring and response capabilities. Many of these engagements begin with improving log visibility and identifying gaps in detection.
Why Better Log Visibility Helps Stop Cyber Attacks
Many cyber attacks begin quietly. Attackers often enter a network using stolen credentials or small vulnerabilities that do not immediately trigger alarms.
These early activities almost always appear in logs first.
When organizations monitor the right logs, they can detect suspicious activity before attackers gain deeper access to systems.
Better log visibility leads to faster detection. Faster detection leads to faster containment.
Security teams that focus on meaningful signals rather than overwhelming data are far better prepared to stop attacks before serious damage occurs.
FAQ About Security Logs
What are security logs in cybersecurity?
Security logs are records that track activity inside systems and networks. They include login attempts, file access, network connections, and configuration changes.
Which logs are most important for threat detection?
Authentication logs, network traffic logs, endpoint activity logs, and cloud access logs are some of the most valuable sources for detecting suspicious activity.
Why do organizations struggle with log monitoring?
Many organizations collect too many logs without filtering or prioritizing them. This creates alert fatigue and makes it harder for analysts to identify real threats.
Strengthen Your Threat Detection Strategy
Security logs can either provide valuable insight or create overwhelming noise. The difference depends on how organizations collect, prioritize, and analyze these records.
When companies focus on the logs that reveal real attacker behavior and combine them with continuous monitoring, they gain faster threat detection and stronger incident response.
Organizations looking to improve their visibility and response capabilities often start by reviewing how their logs are collected, monitored, and investigated. Experienced cybersecurity teams can help identify gaps in monitoring and strengthen detection strategies.
If your organization wants to improve log monitoring, threat detection, or incident response readiness, the Vancord cybersecurity team can help.
Contact the Vancord team.