
Most businesses do not suddenly outgrow their security. It happens slowly. New employees join, systems expand, and more data gets stored. What once felt simple and secure starts to stretch. At first, nothing breaks. Then small issues appear. Alerts get missed. Access becomes harder to track. Risk grows quietly in the background. This is where many organizations are today. Not unprotected, but not fully protected either. In this post, we break down the clear signs your business has outgrown basic IT security and what that really means for your next step.
When Basic IT Security Stops Keeping Up
There is nothing wrong with starting simple.
Antivirus, a firewall, and basic policies are enough for a small team with limited systems.
But most businesses do not stay small.
More people means more devices. More software means more entry points. More data means more risk.
Attackers look for this exact moment. A growing company that has valuable data but has not yet upgraded its security approach.
According to the Verizon Data Breach Investigations Report, small and mid-sized businesses are now heavily targeted, with human error and credential misuse leading many attacks.
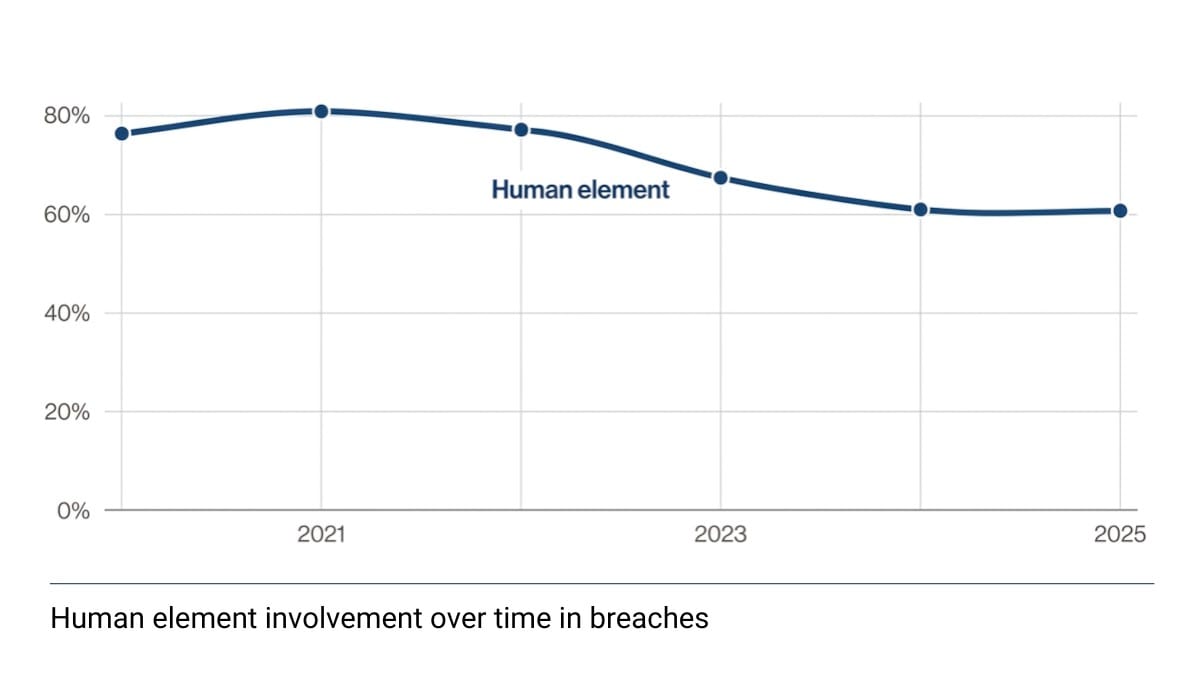
Source: Verizon Data Breach Investigations Report
Basic tools do not address these risks on their own.
You Are Getting More Alerts Than You Can Handle
At first, alerts feel helpful.
They show that your systems are working.
But over time, the number of alerts grows. Emails, warnings, notifications from multiple tools.
It becomes too much.
Some alerts are ignored. Others are delayed. Teams start to assume most are false alarms.
This is known as alert fatigue, and it is one of the most common signs that security has outgrown its setup.
Without a clear process and continuous monitoring, important threats can be missed.
This is where a structured approach like a Security Operations Center (SOC) becomes critical, helping filter noise and focus on real risks.
A Quick Snapshot: Basic vs Advanced Security
To make this easier to understand, here is how basic security compares to a more mature approach:
| Area | Basic IT Security | Advanced Security |
|---|---|---|
| Monitoring | Alerts only | Continuous monitoring with response |
| Visibility | Limited to devices | Full visibility across systems and users |
| Response | Manual, delayed | Immediate, structured response |
| Ownership | Shared IT responsibility | Dedicated security leadership |
| Risk Management | Reactive | Proactive and ongoing |
If your business is moving from left to right in this table, you are already feeling the shift.
Your Team Has Grown But Your Security Hasn’t
One of the clearest signs is headcount. When a company doubles or triples its staff, especially with remote or hybrid employees, the number of devices, logins, and access points multiplies at the same time. Every new person is a new potential point of entry for an attacker, whether through a weak password, a phishing email, or an unsecured home network.
Basic security setups usually don’t include anything that monitors what users are actually doing across the network, or that flags suspicious login behavior in real time. That’s a gap. Proper identity and access management becomes a real need once you have more than a handful of people handling sensitive data, and yet many companies wait until after an incident to address it.
You Are Storing More Sensitive Data Than Before
Think about what your business holds today compared to two or three years ago. Customer payment information, employee records, contracts, healthcare data, financial records. As the scope of what you store grows, so does what’s at stake if something goes wrong.
Basic security tools weren’t built with large data environments in mind. They don’t give you visibility into which files are being accessed, by whom, or whether any of that activity looks unusual. If you’re now storing data that customers or partners are trusting you to protect, the security layer over that data needs to match the responsibility.
According to IBM Cost of a Data Breach Report 2025, the financial impact of breaches continues to grow, especially when sensitive data is involved.
This is often the point where businesses start looking at continuous vulnerability management as a way to get a clearer picture of where their exposure actually sits, rather than just hoping nothing slips through.
You’ve Moved to the Cloud but Haven’t Secured It
The Cloud is a fantastic location for workloads that drive collaboration and increase flexibility. But moving to Microsoft 365, cloud storage, or hosted applications doesn’t automatically mean those environments are secure. In fact, cloud misconfiguration has become one of the most common causes of data exposure. People assume the cloud provider handles security, when in reality a lot of that responsibility sits with the business using the platform.
If your team moved to cloud tools quickly without a plan to lock down permissions, manage access, and monitor activity, there’s a good chance something is configured in a way it shouldn’t be. Cloud and M365 security is its own area of expertise, and it’s one that basic IT setups rarely cover well.
You Have Had Close Calls That Felt “Minor”
Sometimes the biggest warning signs are the ones that did not turn into disasters.
A phishing email almost clicked. A strange login. A vendor account issue.
These are not random. They are signals.
In real-world environments, early detection is what prevents larger incidents. Vancord’s case studies show how unusual activity detected early can be contained before it spreads.
If your current setup can detect something but cannot respond quickly, that is a gap.
Security Is Not Anyone’s Main Responsibility
In many growing businesses, security is handled by the IT team alongside everything else.
That works until it does not.
As systems grow, security becomes too complex to manage part-time.
Policies become outdated. Monitoring becomes inconsistent. Response slows down.
This is where structured leadership, such as a Virtual ISO (vISO), becomes important. It brings focus without requiring a full-time executive hire.
Your Industry Now Has Compliance Requirements
Regulations have a way of changing the conversation fast. If your business operates in healthcare, finance, defense contracting, or education, you’re likely subject to compliance frameworks that basic IT security doesn’t come close to satisfying. HIPAA, CMMC, NIST, and similar standards require documented controls, regular audits, and provable security practices, none of which a standard firewall covers.
Getting ahead of compliance requirements with a cybersecurity readiness assessment is almost always cheaper and less stressful than trying to catch up after a regulator comes knocking. And the benefit goes beyond just avoiding fines. Demonstrating strong security practices builds trust with customers, partners, and vendors who increasingly ask about it before doing business.
You Only React to Problems Instead of Preventing Them
This is one of the most common signs.
Security actions only happen after something goes wrong.
A phishing attempt. A system issue. A flagged vulnerability.
Then action is taken.
According to the Cybersecurity and Infrastructure Security Agency, many successful attacks rely on known vulnerabilities that were never addressed in time.
A mature approach shifts from reacting to preventing. It runs continuously in the background.
What Businesses Do When They Outgrow Basic Security
They do not just add more tools.
They change how security works.
They move toward continuous monitoring, faster response, and clear ownership.
They focus on visibility and consistency.
They build systems that work every day, not just during incidents.
This often includes centralized monitoring, vulnerability management, and structured response processes working together.
FAQ: Signs You Have Outgrown Basic IT Security
How do I know if basic security is no longer enough?
If your business has grown in people, systems, or data and security has not changed with it, it is likely time to upgrade your approach.
Is this only a problem for large companies?
No. Many mid-sized businesses face the biggest gaps because they grow quickly without adjusting security.
Do we need a full internal security team?
Not always. Many organizations use managed services to extend their capabilities without adding internal overhead.
What is the first step to improving security?
Start with a clear understanding of your current risks. A structured assessment helps identify gaps and priorities.
It Might Be Time to Rethink Your Security Approach
Growing out of basic security isn’t a failure. It’s actually a sign that your business has built something worth protecting more carefully. The next step is figuring out exactly where the gaps are and what the right level of protection looks like for where you are now.
Vancord has spent two decades helping mid-to-large organizations across New England match their security posture to their actual risk. If something in this post sounds familiar, it’s worth having a no-pressure conversation about what’s changed in your environment and whether your current setup is keeping pace.
Talk to Vancord’s security team or request a security assessment to get a clear picture of where your business stands today.